Your APIs handle millions of requests daily. They're also your biggest security blindspot.
99% of organizations encountered API security problems in 2025. The average API breach costs enterprises $4.9 million. Yet most security teams treat APIs as an afterthought.
The gap between API growth and security maturity is dangerous. Here's what works.
The Current API Security Crisis
Enterprise API incidents increased 681% over the past 12 months. The numbers tell a stark story:
- 22% of organizations experienced an API-related breach
- Only 27% have visibility into sensitive data exposed via APIs
- 80% use weak controls like static API keys or basic OAuth
The problem isn't just technical. It's strategic. APIs multiply your attack surface faster than security teams can secure them.
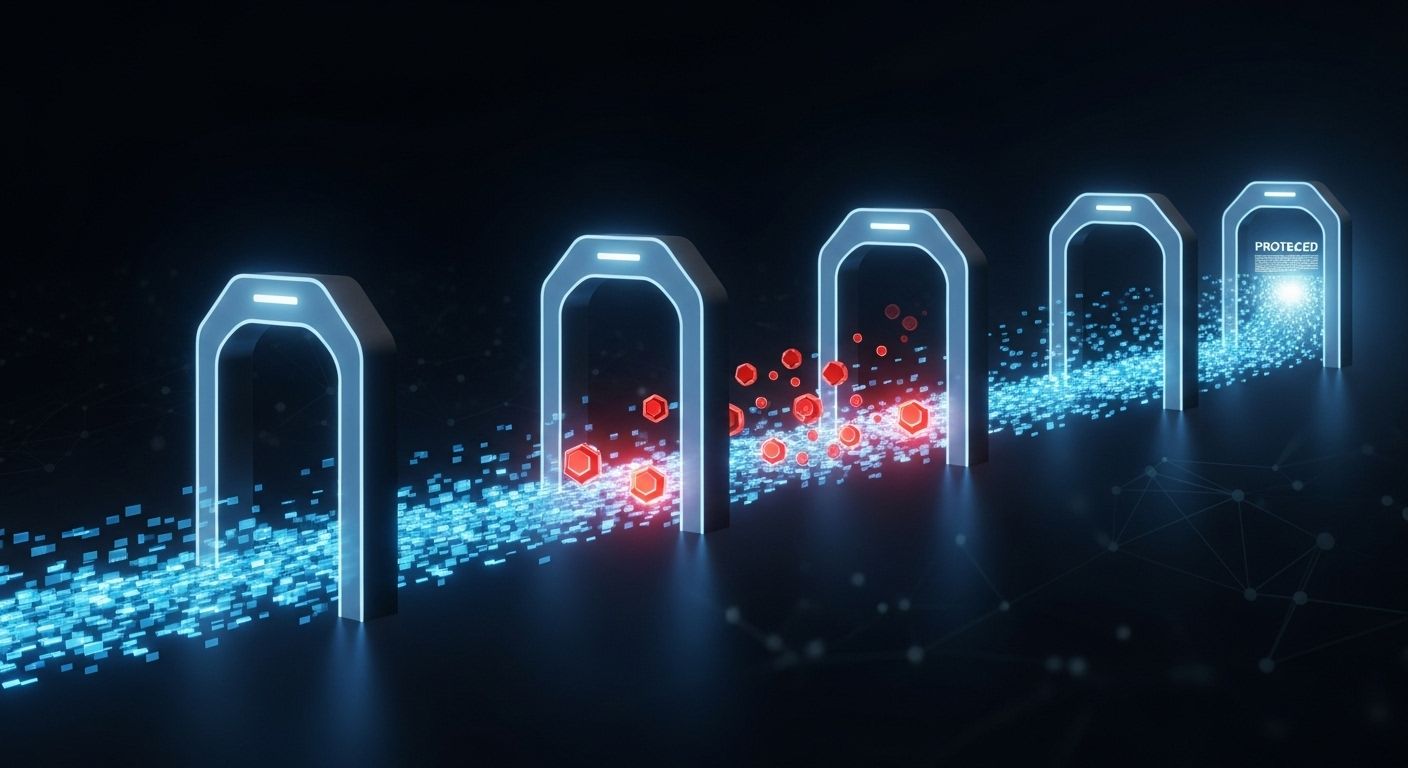
Best Practice 1: Implement Zero Trust Authentication
Traditional perimeter security fails with APIs. Zero Trust assumes every request is potentially malicious.
- Every request requires authentication and authorization
- No permanent trust - continuous verification
- Identity verification happens at every endpoint
What Zero Trust means for APIs:
NIST's 2025 guidelines recognize API gateways as "identity translators." They convert diverse credential types - certificates, mTLS, Kerberos, API keys - into standardized forms.
- Deploy API gateway with centralized authentication
- Require multi-factor authentication for sensitive endpoints
- Use short-lived tokens (15-60 minutes maximum)
- Implement continuous authorization checks
Implementation approach:
Companies using Zero Trust architecture experience 58% lower breach costs than those with traditional security models.
Best Practice 2: Deploy Intelligent Rate Limiting
Rate limiting prevents both accidental overload and malicious attacks. But simple rate limits aren't enough.
- Dynamic limits based on user behavior
- Geographic restrictions for suspicious regions
- Time-based limits for different operations
- Adaptive thresholds that respond to attack patterns
Modern rate limiting includes:
API rate limiting prevents DDoS attacks where attackers flood services with requests. Advanced systems adjust limits in real-time based on:
- Historical usage patterns
- Current system capacity
- Threat intelligence feeds
- User authentication status
- Authenticated users: 1000 requests/hour
- Anonymous users: 100 requests/hour
- Suspicious IPs: 10 requests/hour
- During attacks: Progressive reduction
Configuration example:
Best Practice 3: Enforce Proper Object-Level Authorization
Broken Object Level Authorization (BOLA) remains the #1 API security risk in OWASP's 2023 rankings. Users access objects they shouldn't see.
- APIs don't verify ownership before returning data
- Object IDs are sequential and guessable
- Authorization checks happen only at endpoint level
- User context isn't validated for each object
BOLA occurs when:
- Validate object ownership on every request
- Use random, non-sequential object identifiers
- Implement context-aware authorization
- Never rely on client-side filtering
Prevention strategies:
Code-level protection: Instead of trusting the user ID from the token, validate ownership:
// Vulnerable
GET /api/users/123/orders
// Secure
GET /api/users/current/orders
// Backend validates token user matches requested userBest Practice 4: Implement Comprehensive Monitoring
You can't secure what you can't see. API monitoring requires different approaches than traditional application monitoring.
- Real-time request analysis
- Anomaly detection for unusual patterns
- Payload inspection for malicious content
- Authentication failure tracking
Essential monitoring components:
AI-powered threat detection revolutionizes API security through:
- Behavioral analysis: Establishes baseline usage patterns
- Predictive security: Machine learning predicts vulnerabilities
- Automated response: Implements countermeasures in real-time
- Failed authentication attempts exceeding thresholds
- Requests from new geographic locations
- Unusual data access patterns
- Requests to deprecated or internal endpoints
Monitoring alerts should trigger on:
Modern API security platforms detect 80% of attacks using OWASP Top 10 methods, but only 53% of organizations focus on this industry-standard framework.
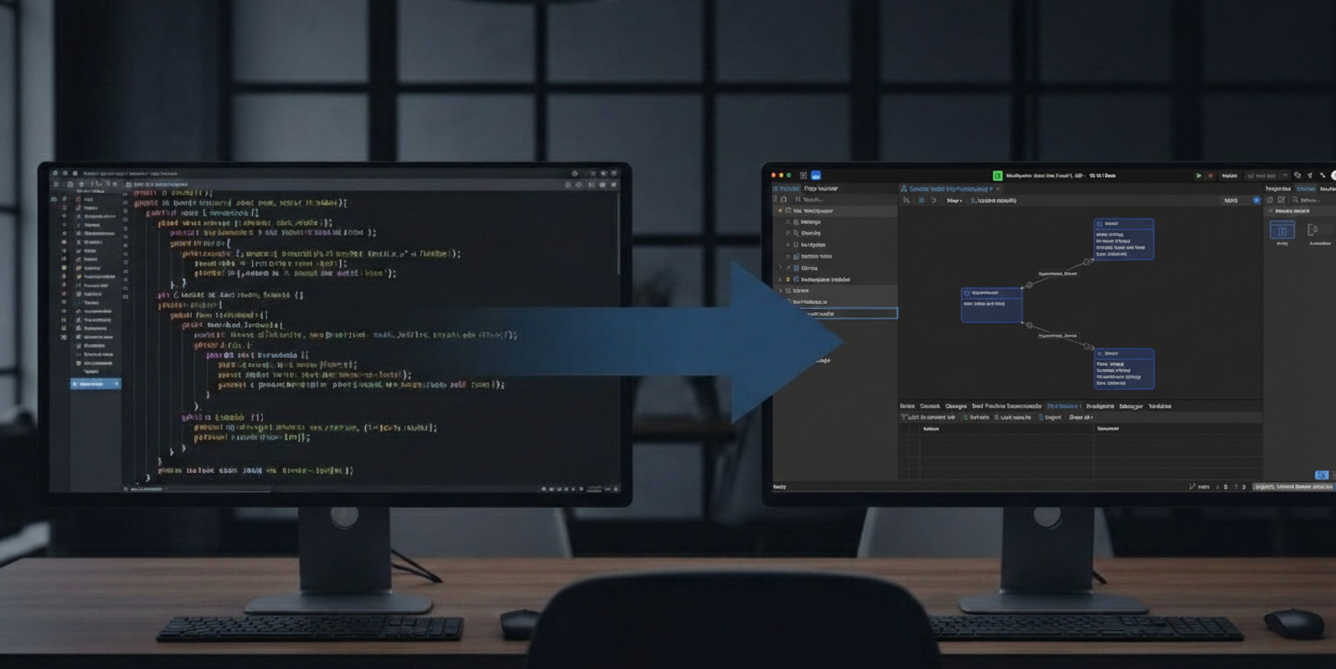
Best Practice 5: Secure API Development Lifecycle
Security can't be bolted on after development. It requires integration throughout the API lifecycle.
- Threat modeling for each new API
- Security requirements in design specifications
- Code review focused on authorization logic
- Static analysis for common vulnerabilities
Development phase security:
- Dynamic Application Security Testing (DAST) scans running APIs
- Penetration testing of authentication mechanisms
- Fuzzing to discover input validation flaws
- Load testing with security scenarios
Testing phase requirements:
- Automated security scans in CI/CD pipelines
- Configuration validation against security policies
- TLS certificate management and rotation
- Environment-specific security controls
Deployment security:
- Continuous vulnerability scanning
- Regular security assessments
- Incident response procedures
- Security metrics and reporting
Production security:
Organizations with mature API security programs experience 58% lower breach costs compared to those with minimal security measures.
Implementation Timeline
Start with the highest-impact practices first:
Week 1-2: Deploy API gateway with basic authentication and rate limiting Week 3-4: Implement zero trust authentication for critical endpoints Week 5-6: Add comprehensive monitoring and alerting Week 7-8: Enhance authorization with object-level controls Week 9-12: Integrate security throughout development lifecycle
The key is starting immediately. API security incidents are accelerating, but enterprises with proactive security programs significantly reduce both risk and financial impact.
Strategic Security Architecture
Enterprise API security succeeds when technology meets operational expertise. The right approach balances technical controls with business requirements, ensuring security doesn't impede digital transformation goals.
Organizations implementing comprehensive API security see measurable improvements: reduced incident response time, lower compliance costs, and increased confidence in digital initiatives. The investment in proper API security pays for itself through avoided breach costs alone.
At Bonjoy, we've guided enterprises through complex API security decisions, focusing on practical implementation that balances security requirements with operational realities. Strategic technology decisions require understanding both current vulnerabilities and emerging threat patterns.